The flexibility offered by coworking spaces can be alluring, but many customers have security concerns about working in a space with others. How can you be sure that your computer and data are secure while you’re working in a shared office? In this blog we’ll explore some of the ways Thrive Workplaces are set up to help you stay safe and secure in our offices.
Thrive’s connectivity
As with permanent offices, Thrive offer both wired and wireless connectivity to our customers. This means you can connect a variety of different devices and equipment to enable you to work efficiently and easily in a way that suits you.
If you’re a solo worker with a single laptop or tablet, getting started couldn’t be easier – just connect your device to our Member Wi-Fi and enjoy safe Internet connectivity.
However, some of our larger or longer-term customers bring a whole office of equipment to our spaces, including specialist printers, scanners and desktop servers as well as laptops, tablets and mobile phones.
Such an array of devices can bring challenges when it comes to hooking everything up, so at Thrive we’ve built our networks to ensure that not only can all your devices talk to one another, but that they do so securely.
How does Thrive do things?
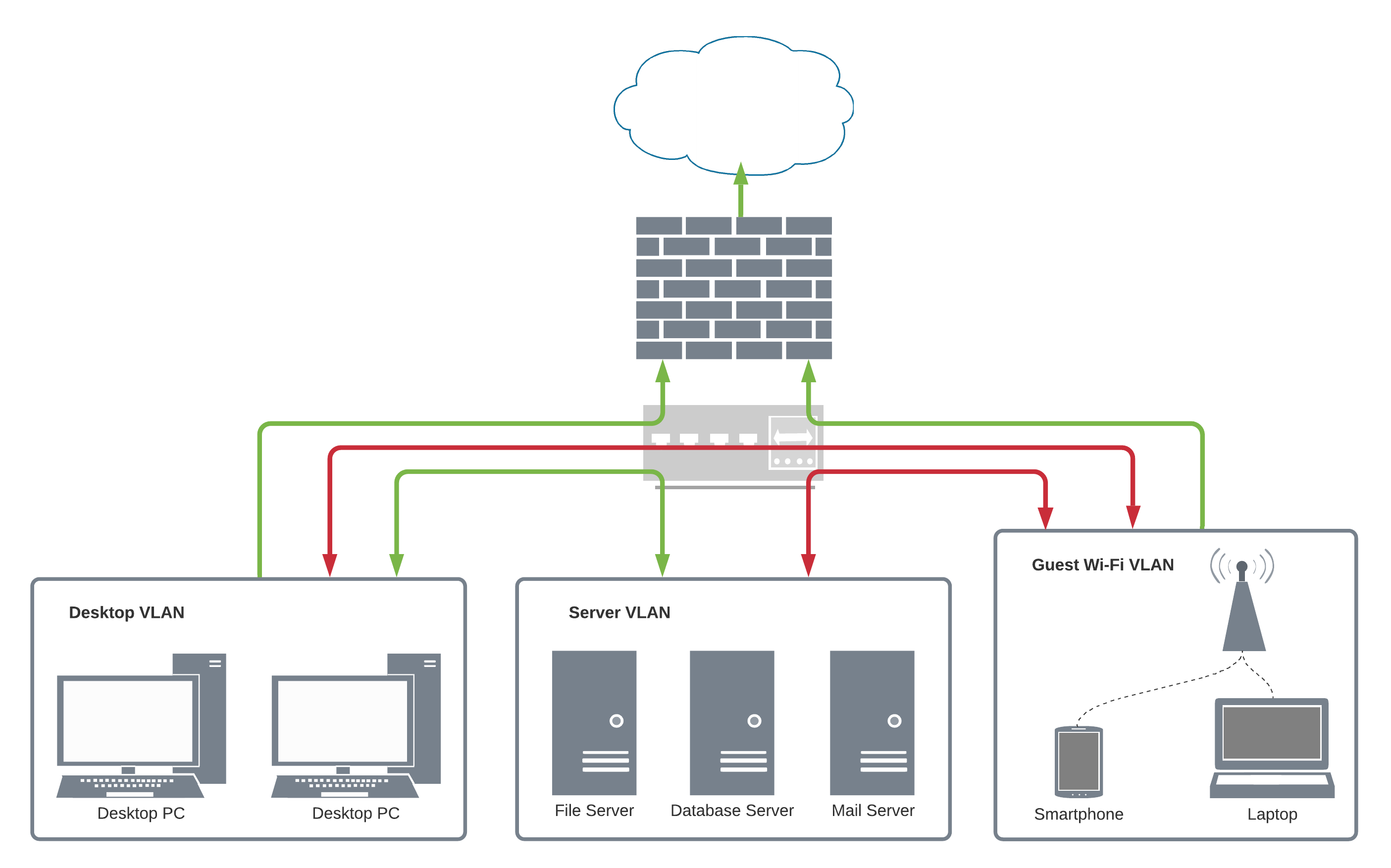
One of the main technologies we use to achieve network security and customer separation is VLANs – Virtual Local Area Networks.
First, we need a little background: a basic computer network is commonly referred to as a LAN, or Local Area Network. On a LAN, all the connected computers, printers and servers can talk to each other and pass data between themselves.
This is simple to set up and great for productivity but if a hacker or rogue employee gets control of a computer to do something malicious, there’s not much to stop them connecting to all the other computers on the network. Our Member Wi-Fi separates individual devices by their unique IP address and ensures they can only talk to the Internet and certain Thrive devices, while Guests are completely separated from the rest.
However, some additional configuration is required if you need multiple devices to talk to each other, and we achieve this using VLANs. VLANs group together IP addresses and subnets that can talk amongst themselves, and in doing so break up the LAN into smaller virtual networks, even if they use the same underlying network equipment. This is where the term Virtual LAN comes from.
Access from one VLAN to another can be tightly controlled, allowing for network segmentation based on locations, type of device, departments or other determining factors. Traffic being passed inside each VLAN doesn’t cross into other parts of the network unless it’s allowed to, which reduces traffic across the network as a whole and prevents devices talking to others elsewhere on the network.
Enough theory, how does this work in real life?
In a company network, the IT Department may set up VLANs for desktops in different offices or departments, one for the Guest Wi-Fi, and one for servers. Using VLAN access control lists, a computer on the Desktop VLAN can talk to the Server VLAN but may be unable to reach devices on the Guest Wi-Fi VLAN. Similarly, the Guest Wi-Fi VLAN can be configured so that it’s unable to reach either the servers or the desktops and is only allowed to reach the Internet.
At Thrive we use Cisco’s Meraki technology to underpin our networks. This platform allows a unique VLAN to be assigned to a customer, creating a small dedicated virtual network for their devices to communicate with each other.
As well as ensuring your device is separated from others in the workspace, this means that for many of our customers there’s no need to bring additional network equipment, such as routers. Adding a router to a shared network can cause IP address clashes, routing problems and other network-level issues that may hinder your productivity or affect others.
What if I need to bring lots of equipment?
For those customers who do need to bring more extensive equipment to our Workplaces, or those who plan to use us for longer periods of time, we offer additional services to help them get set up so that these devices are able to talk securely among themselves on their own VLANs.
As well as free basic onboarding and initial connection to the Member Wi-Fi as part of our Standard package, we also offer a Standard+ network onboarding package to help those larger customers, which includes configuring a dedicated VLAN. For more extensive assistance with designing and implementing your network, we can also tailor a Custom package to your needs, with advanced configuration and dedicated public IP address options.
Ask us about our additional services and see how we can help you!
Here are some other ways you can help make sure you’re working safely and securely from anywhere:
- Have an up-to-date anti-malware tool installed on your computer
- Ensure your laptop’s built-in firewall is turned on
- Have a password on your computer and make sure you can lock it in case you have to leave it unattended
- Consider encrypting the hard drive in your computer – Windows’ BitLocker and MacOS’ FileVault are both able to do this natively with no extra software
- Use multi-factor authentication on your email and other online services
- Store your data on a cloud-based storage platform such as OneDrive, Google Drive or Dropbox


